AQSACOM now delivers ALIS, its Lawful Cyber Interception System, to virtualized network function architectures.
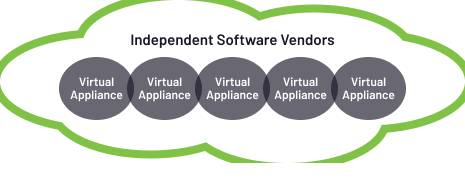
AQSACOM delivers ALIS, its Lawful Cyber Intelligence System, to virtualized network function architectures. Network Functions Virtualization (NFV) essentially decouples an infrastructure-based service from the physical assets on which that service operates. As such, a service is not strictly associated with any physical asset.
Instead, the service is described in a data structure and exists entirely in a software abstraction layer reproducing the service on any physical resource running the virtualized software. The life cycle, identity, location, and configuration attributes of the service exists in software with APIs (application programming interfaces), thereby unlocking the full potential of automated provisioning.
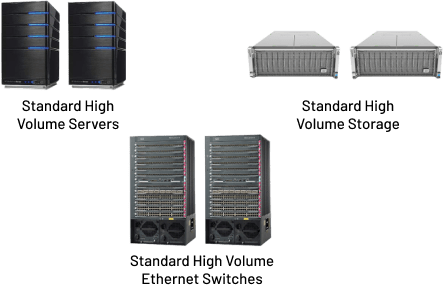
AQSACOM’s virtualized solutions is deployed as a software-based solution. It can be readily integrated into any virtualized network. AQSACOM’’s virtualization’s main goals are:
AQSACOM takes an evolutionary approach to its implementation of its solutions over virtualized networking environments. This matches carrier strategies as they likewise evolve their networks to virtualized function architectures.
AQSACOM’s virtualized offerings allow rapid customization, the development of new features, flexible settings, and complete operational transparency while readily interacting with other, third-party software

As indicated in Figure 1, a wide range of network functions can be shifted to a virtualized environment. AQSACOM considers Lawful Interception (LI) as one of many network functions, now in a new setting.